Like the title says, I upgraded my nixos-unstable after 3 weeks and now gpg -d foo.gpg tells me:
gpg: public key decryption failed: No pinentry
gpg: decryption failed: No secret key
Did anything change with regards to gpg or pinentry?
Like the title says, I upgraded my nixos-unstable after 3 weeks and now gpg -d foo.gpg tells me:
gpg: public key decryption failed: No pinentry
gpg: decryption failed: No secret key
Did anything change with regards to gpg or pinentry?
pinentry has been disabled by default. The commit includes a release note saying
GnuPG is now built without support for a graphical passphrase entry by default. Please enable the
gpg-agentuser service via the NixOS optionprograms.gnupg.agent.enable. Note that upstream recommends usinggpg-agentand will spawn agpg-agenton the first invocation of GnuPG anyway.
@lilyball Yep, thanks, that worked perfectly!
This doesn’t change anything for me, despite of programs.gnupg.agent.enables value, I get the pinentry error.
this worked after reboot
Just installed nixos and for me it has never worked.
The problem appears to be that no matter what I say in configuration.nix, the gpg-agent ignores my ~/.gnupg/gnupg-agent.conf and only looks for the pinentry in the same store path where gpg itself resides.
Which renders me completely unable to get any prompt (no matter whether it’s graphical or tty).
A workaround was to disable gpg-agent system wide and manually start the agent with everything user-installed (i.e. pinentry and gnupg)
@ppenguin Did you ever solve this? I found a helpful post online
https://sigkill.dk/writings/guides/nixos_pass.html
But this sucks. A better solution is to install
pinentry-curses(put it in yoursystemPackagesin your NixOS configuration), and then modify$HOME/.gnupg/gpg-agent.confto contain the following:pinentry-program /run/current-system/sw/bin/pinentry-cursesYou may need to reload the running
gpg-agentto make it pick up the change:$ gpgconf --reload gpg-agent
When switching WMs it has always been a PITA, especially when not using a display manager for login to take care of the session env. But I’ve been using home-manager in combination with services.gnome-keyring and start my wayland compositor like this:
zsh.loginExtra = ''
if [ "$(tty)" = "/dev/tty1" ]; then
QT_QPA_PLATFORM=wayland
LIBSEAT_BACKEND=logind
TERMINAL=alacritty
export QT_QPA_PLATFORM LIBSEAT_BACKEND TERMINAL
SSH_AUTH_SOCK=/run/user/$UID/keyring/ssh
export SSH_AUTH_SOCK
dbus-update-activation-environment --systemd --all
echo "$(date -Is): starting Hyprland..." >> $HOME/.wsession.log
Hyprland &> /dev/null
echo "$(date -Is): Hyprland stopped" >> $HOME/.wsession.log
systemctl --user stop hyprland-session.target
logout
fi
'';
and in configuration.nix I have
security = {
pam.services = {
login = {
# startSession = true;
enableGnomeKeyring = true;
};
# gnome keyring even without display manager
logind.enableGnomeKeyring = true;
# sshd.enableGnomeKeyring = true;
};
polkit = {
enable = true;
};
};
and that makes it work. I’m not sure whether/where there is overlap there, and I really hate how messy and unclear this all is, but I’m reluctant to touch it again ![]()
EDIT:
Oops, of course most of that was actually for the ssh-agent, I also have gpg-agent via home-manager. Go figure.
services.gpg-agent = {
enable = true;
defaultCacheTtl = 1800;
enableSshSupport = false; # we want the normal SSH_AUTH_SOCK=/run/user/1000/keyring/ssh
pinentryFlavor = "gnome3";
};
but come to think of it I haven’t seen a popup in ages, so I guess that means gnome-keyring is actually doing its job?
In the end I wouldn’t settle for anything less than having my keyring unlocked by logging into my user session and never having to enter gpg or ssh passwords during a normal session.
Thank you, it works fine although I’ve encountered this issue :
[info] gpg: signing failed: Inappropriate ioctl for device
[info] gpg: signing failed: Inappropriate ioctl for device
[error] java.lang.RuntimeException: Failure running 'gpg --detach-sign ...
because in my case gpg is run in background… execution controlled by the build tool. I’ve executed the command by hand in order to have the passphrase being taken into account and restart the full build tool process.
I’ll have to switch to the gtk3 approach I guess
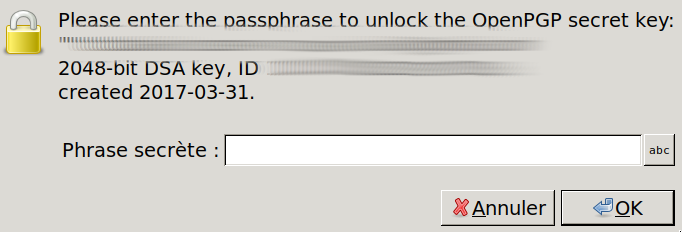
Added in ~/.gnupg/gpg-agent.conf :
pinentry-program /run/current-system/sw/bin/pinentry-gtk-2
Use nix configuration :
services.pcscd.enable = true;
programs.gnupg.agent = {
enable = true;
#pinentryFlavor = "curses";
pinentryFlavor = "gtk2";
enableSSHSupport = true;
};
With the following packages installed : gnupg pinentry-curses pinentry-gtk2 (I kept pinentry-curses as I will use it for other purposes)